You can set actions to automatically pull the new image version/digest or notify you of its release. The actions can be tailored to specific image lines or to respond to vulnerabilities of certain severity or exploitability labels.Documentation Index
Fetch the complete documentation index at: https://docs.minimus.io/llms.txt
Use this file to discover all available pages before exploring further.
Overview
As a rule, actions only apply to images included in your Minimus subscription. There are 2 steps to configuring an action:- Decide when to set off the action, that is, what the action should respond to. The following triggers are supported:
- New image version/digest
- Vulnerability fix
- Image line nearing EOL
- Image line reached EOL
- EOL image was pulled
- Decide what the response should be, that is, what the action should do. The following responses are supported:
- Trigger a webhook
- Send email
- Send Slack alert
- Trigger GitHub Action
When to trigger the action
By new version/digest release
You can set an action to trigger in response to a new version release or a new image digest (that is, a new image build following an update as shown in the image changelog).- Select Actions in the left menu. Then select Create Action and fill out the form as follows.
- Name the action.
- When - Select New image version is released. If you prefer, toggle on the option to Alert for every new digest of the same version. When enabled, the action will trigger every time there is a new image build for the relevant image lines. See also digest history and image changelog.
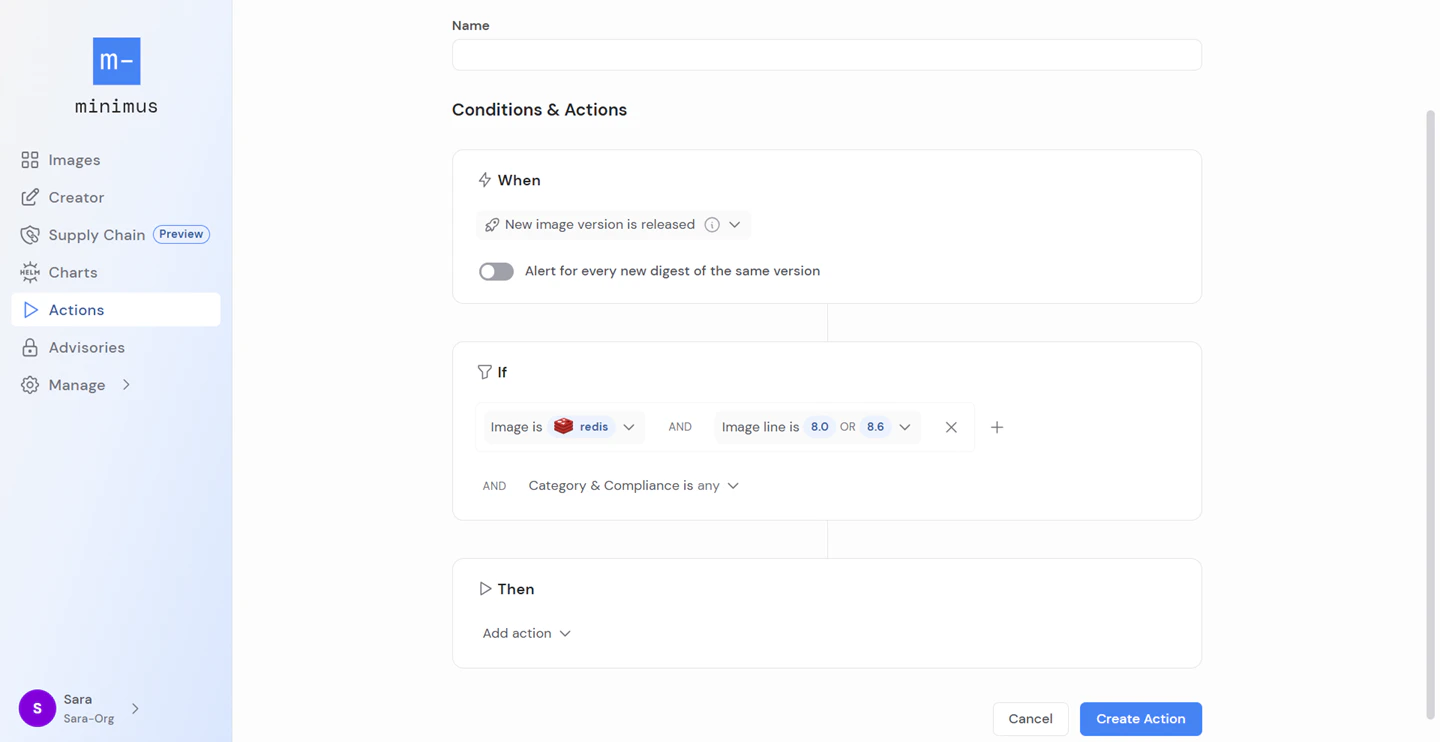
- If - Add your filters. You can filter by image properties and combine as many filters as relevant:
- Select images by name from the list.
Only images included in your subscription will be shown.
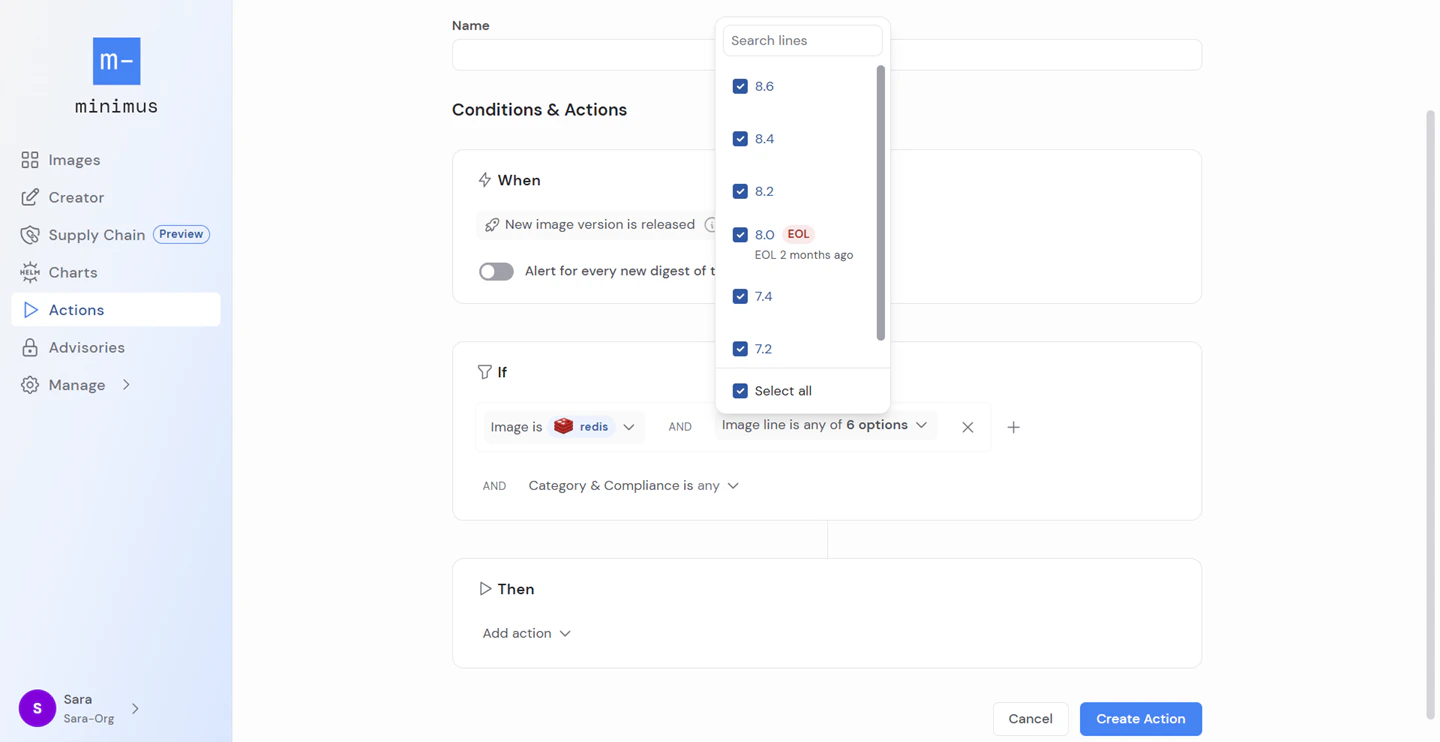
- Select image lines from the list.
End of life (EOL) indications and dates will be shown on lines reaching or post-EOL.
- Instead of selecting specific images by name, you can instead select relevant filters from the image category & compliance. Compliance may be FIPS or STIG compatibility.
- Select images by name from the list.
- Then - select the action and proceed as explained below.
By vulnerability fix
You can set an action to trigger in response to a vulnerability fix.- Select Actions in the left menu. Then select Create Action and fill out the form as follows.
- Name the action.
- When - Select Vulnerability is fixed
- If - Add your filters. You can combine filters for image and vulnerability properties:
- Select images by name from the list.
Only images included in your subscription will be shown.
- Select image lines from the list.
End of life (EOL) indications and dates will be shown on lines reaching or post-EOL.
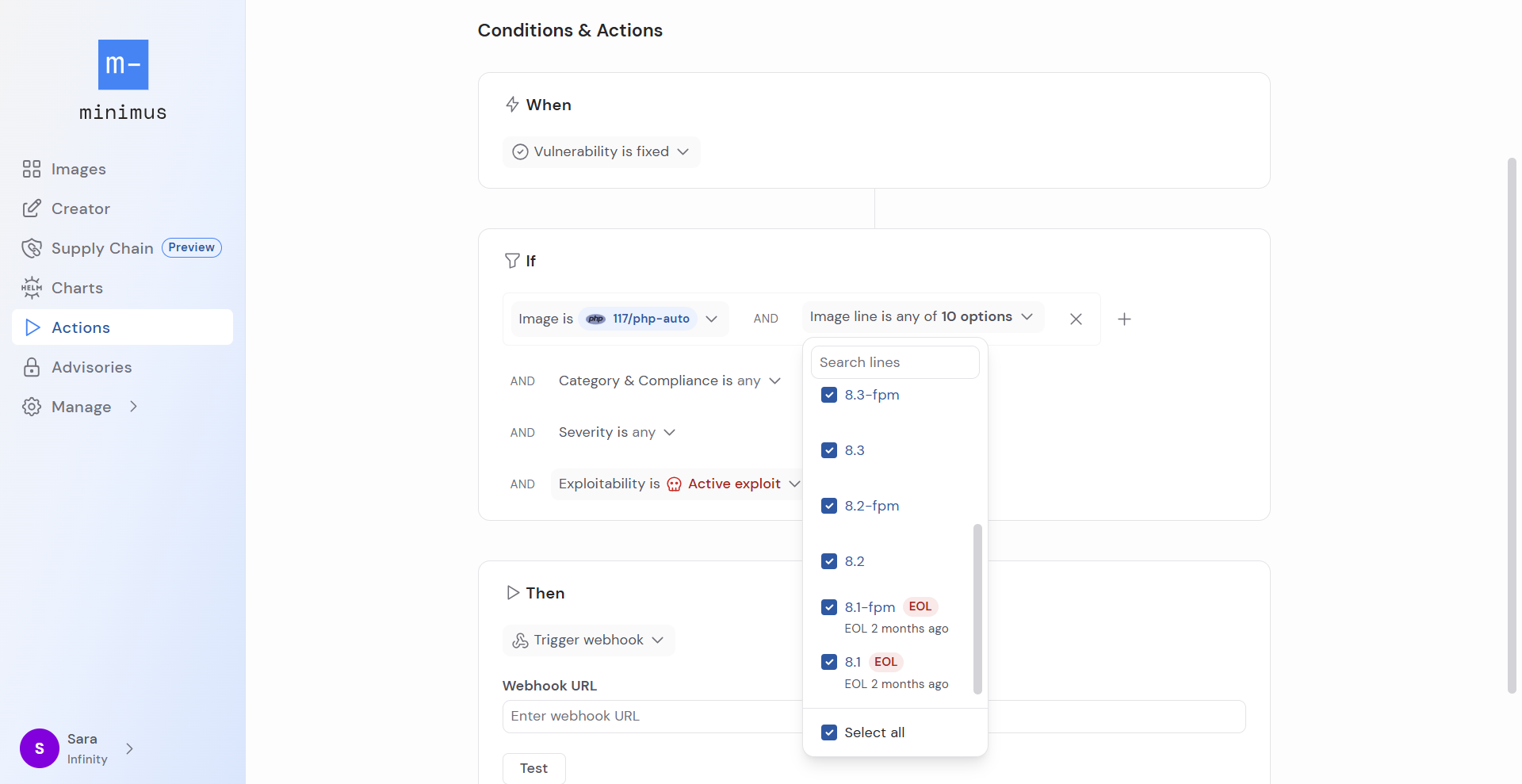
- Instead of selecting specific images by name, you can instead select relevant filters from the image category & compliance. Compliance may be FIPS or STIG compatibility.
- Select vulnerability Severity. You can select unknown, low, medium, high, critical.
- Select Exploitability is either Active exploit, Likely to be exploited, or both.
- Select images by name from the list.
- Then - select the action and proceed as explained below.
By EOL date
EOL notifications run once daily and only alert once per image line to avoid duplicates.- Select Actions in the left menu. Then select Create Action and fill out the form as follows.
- Name the action.
- When - Select one of the following:
- Select Image line nearing EOL. Then decide how many weeks of advance notice you want (1–12 weeks).
Saving the action adds it to the daily queue. The first alert will be sent during the next scheduled notification window, and will list all relevant image lines that have already passed the notification threshold. For example, if you set a 2 week notice, the first alert will notify you of any images that have less than 2 weeks remaining until EOL.
- Select Image line reached EOL.
Saving the action adds it to the daily queue. The first alert will be sent during the next scheduled notification window, and will list all relevant image lines that have reached EOL in the past 90 days.
- Select Image line nearing EOL. Then decide how many weeks of advance notice you want (1–12 weeks).
- If - Add your filters. You can filter by image properties and combine as many filters as relevant:
- Select images by name from the list.
Only images included in your subscription will be shown.
- Select image lines from the list.
End of life (EOL) indications and dates will be shown on lines reaching or post-EOL.
- Instead of selecting specific images by name, you can instead select relevant filters from the image category & compliance. Compliance may be FIPS or STIG compatibility.
- Select images by name from the list.
- Then - select the action and proceed as explained below.
By EOL image pull
Configure actions to trigger when images that have passed end-of-life are pulled.- Select Actions in the left menu. Then select Create Action and fill out the form as follows.
- Name the action.
- When - Select EOL image was pulled
- If - Add your filters. You can filter by image properties and combine as many filters as relevant:
- Select images by name from the list.
Only images included in your subscription will be shown.
- Select image lines from the list.
End of life (EOL) indications and dates will be shown on lines reaching or post-EOL.
- Instead of selecting specific images by name, you can instead select relevant filters from the image category & compliance. Compliance may be FIPS or STIG compatibility.
- Select images by name from the list.
- Then - select the action and proceed as explained below.
Trigger a webhook
- Select the action Trigger webhook
- Add your webhook URL. The webhook client is a simple HTTP client that sends POST requests to the endpoint.
- Test the action.
- If the test is successful, select Create Action to save and enable the action.
About action webhooks
- The webhook provider receives a single event for each alert. Aggregation is not currently supported.
- Here’s an example of the JSON payload schema sent by the action:
JSON payload schema example
Send email notifications
Minimus will send an email notification for every relevant update.- Select the action Send email.
- List recipients (using commas as separators). You can add CC recipients as well.
- Optionally, you can add a custom note. The note will be appended to the default messages.
- Test the action.
- If the test is successful, select Create Action to save and enable the action.
Send Slack alerts
- Select the action Send Slack Alert.
- Click the button Connect to Slack.
- Allow the permissions requested in the popup window. If you are connected to several Slack workspaces, you can select the relevant one from the top right corner.
- The form will now show the connected workspace.
- List the channels to be notified. The Minimus app can send messages to public channels by default. For private channels, you will need to add the Minimus app to the channel in advance.
- Test the action.
- If the test is successful, select Create Action to enable it.
Add the Minimus App to a private Slack channel
If you don’t give the Minimus App permissions to message your private Slack channel, the test will fail with the message “not in channel”.- In your private Slack channel, click the kebab menu in the top right corner.
- Select Edit settings.
- Select the Integrations tab.
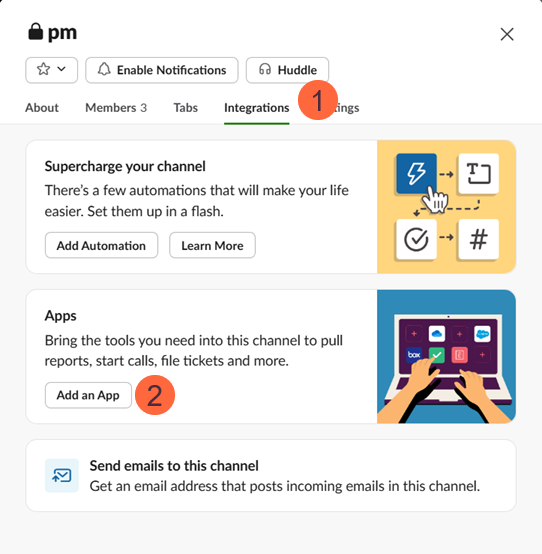
- Add the Minimus App.
- That’s it. Minimus can now notify the channel.
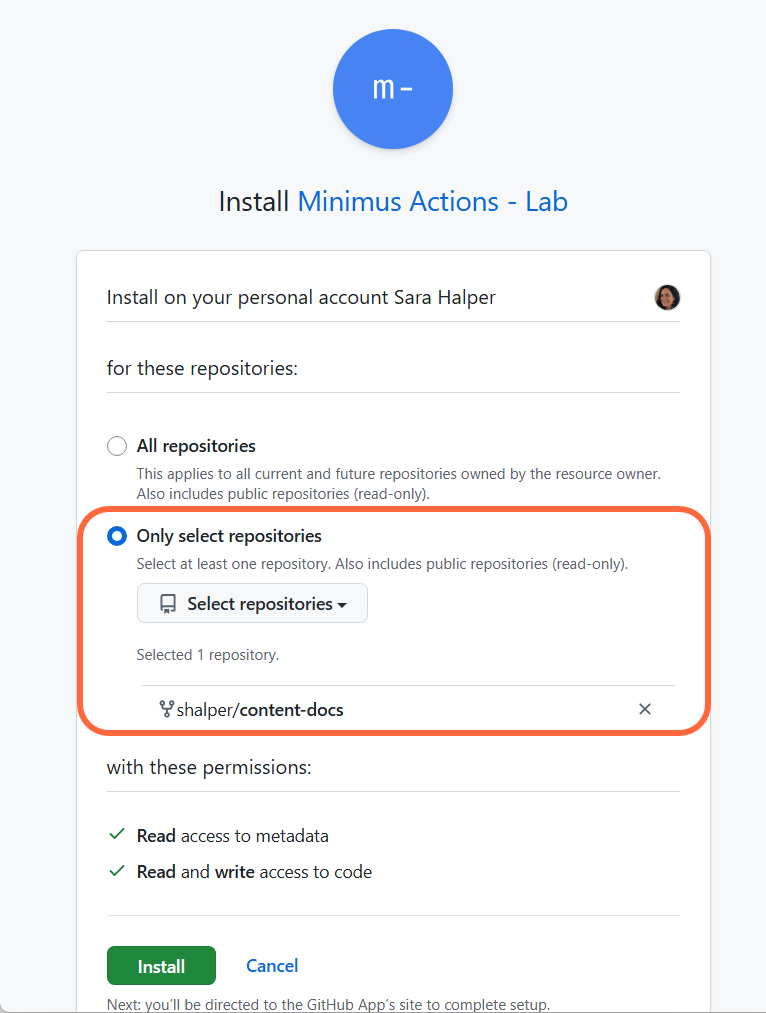
Trigger GitHub Actions
- Select the action Trigger GitHub Actions.
- Click the button Connect to GitHub.
- Select the relevant GitHub owner or organization.
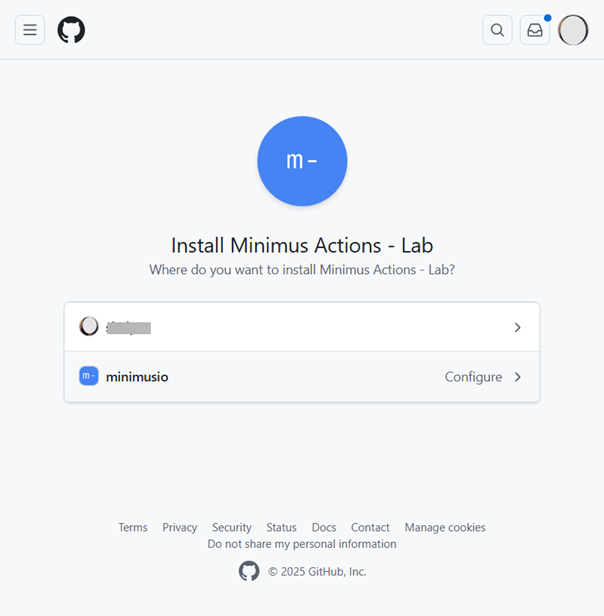
- Specify the Owner and Repository. For example, if your organization’s GitHub URL looks like
https://github.com/myorganization/myproject/- the owner ismyorganizationand the repository ismyproject. - Test the connection.
- If the test is successful, select Create Action to enable it.
Troubleshooting the connection to GitHub
- Scroll down if necessary
If you previously created an action that connected to your GitHub repo, the popup approval window will open in your general GitHub settings menu - https://github.com/settings/profile.- Scroll down until you see the section for configuring Repository access.
- Select the relevant owner and repo as usual and save your selection.
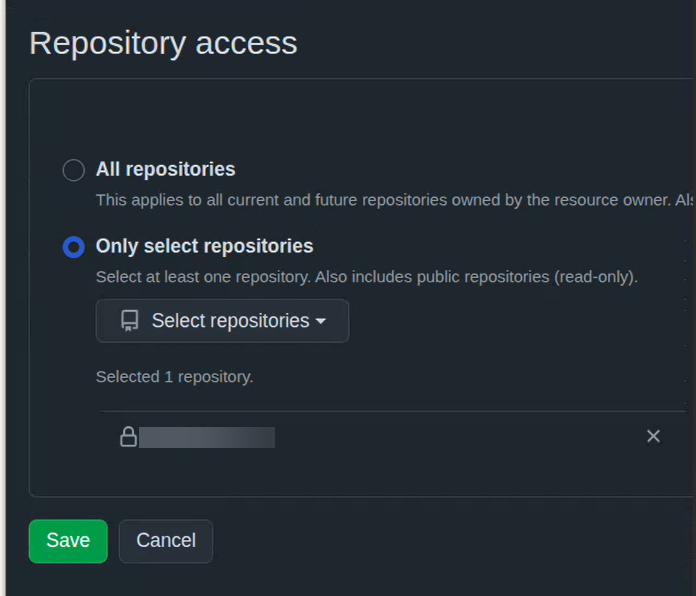
- Reset repository selection if necessary
Sometimes, if you previously created an action that connected to a private GitHub repo, the popup approval window will apply your previous selection. In this case, the Repository access section will appear to be “locked” on your previous selection with the Save button disabled.- To activate the Save button, first change the selection to All repositories.
- Next, select the relevant owner and repository and save your selection.
Note that the relevant configuration is also found in your GitHub settings under https://github.com/settings/installations.