Verify Security Content Automation Protocol (SCAP)
OpenSCAP tools are the recommended toolset for validating the configuration of container images and reviewing the configuration of an image file system. For ease of use, Minimus provides a hardened OpenSCAP image that always includes the most up-to-date package version for all of the included packages and dependencies. Use the Minimus OpenSCAP image to scan your Docker images and containers without the need to install OpenSCAP locally. This image comes preloaded with a Minimus STIG file for security and compliance assessments.How to verify STIG compliance for Minimus images
To test the Minimus OpenSCAP image, follow the steps below to scan an image using its file system.Download OpenSCAP from Minimus
Authenticate to the Minimus registry with your token. Visit the token page in your Minimus console to copy the command with your embedded token:Pull the OpenSCAP latest image from the Minimus registry:
example of docker login command
Download the Data Stream file
The data stream module (ds) is provided by Minimus and used to automatically validate the image or container. Download the file ssg-minimus-gpos-ds.xml from the Minimus public GitHub repo.To pull the file locally:For good measure, verify the file:You should see a printout of file details, beginning with
Document type: Source Data Stream and version information.Create a directory for the scan results
Pull the image to be scanned
Pull the image you plan to scan from the Minimus registry, for example:
Run the OpenSCAP scan
Use the oscap-docker tool to perform offline scanning from the Minimus provided image:
--resultsindicates where to place the XML formatted report--reportindicates where to place the HTML report- The data stream location points to the location of the SCAP source data stream file
XCCDF Format
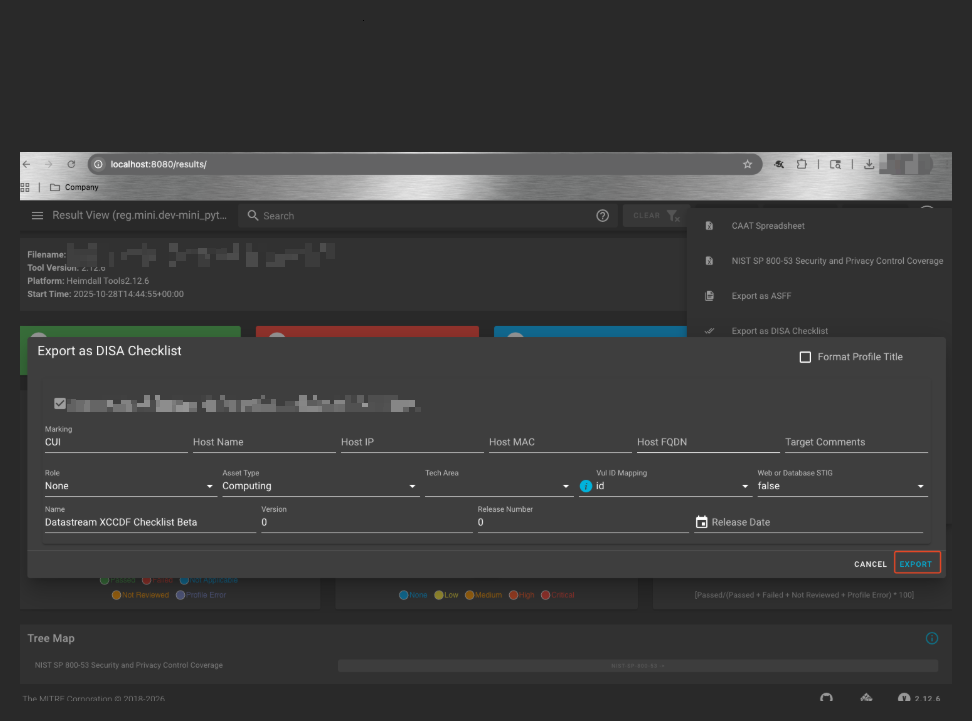
The eXtensible Configuration Checklist Description Format is part of the SCAP standard. OpenSCAP tooling uses XCCDF to automate compliance and configuration remediation. XCCDF STIG reports can be viewed in dedicated viewing tools endorsed by the DoD. Currently, STIG Viewer 3 is the most up to date. The relevant style sheet is bundled with the STIG. (Link to download the STIG Viewer.)Convert DISA STIG XML to other formats
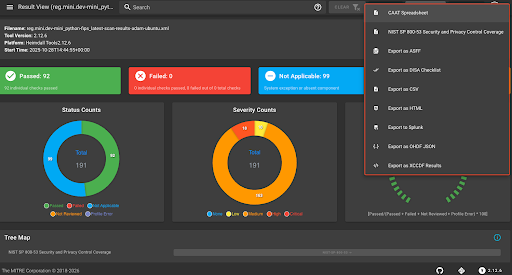
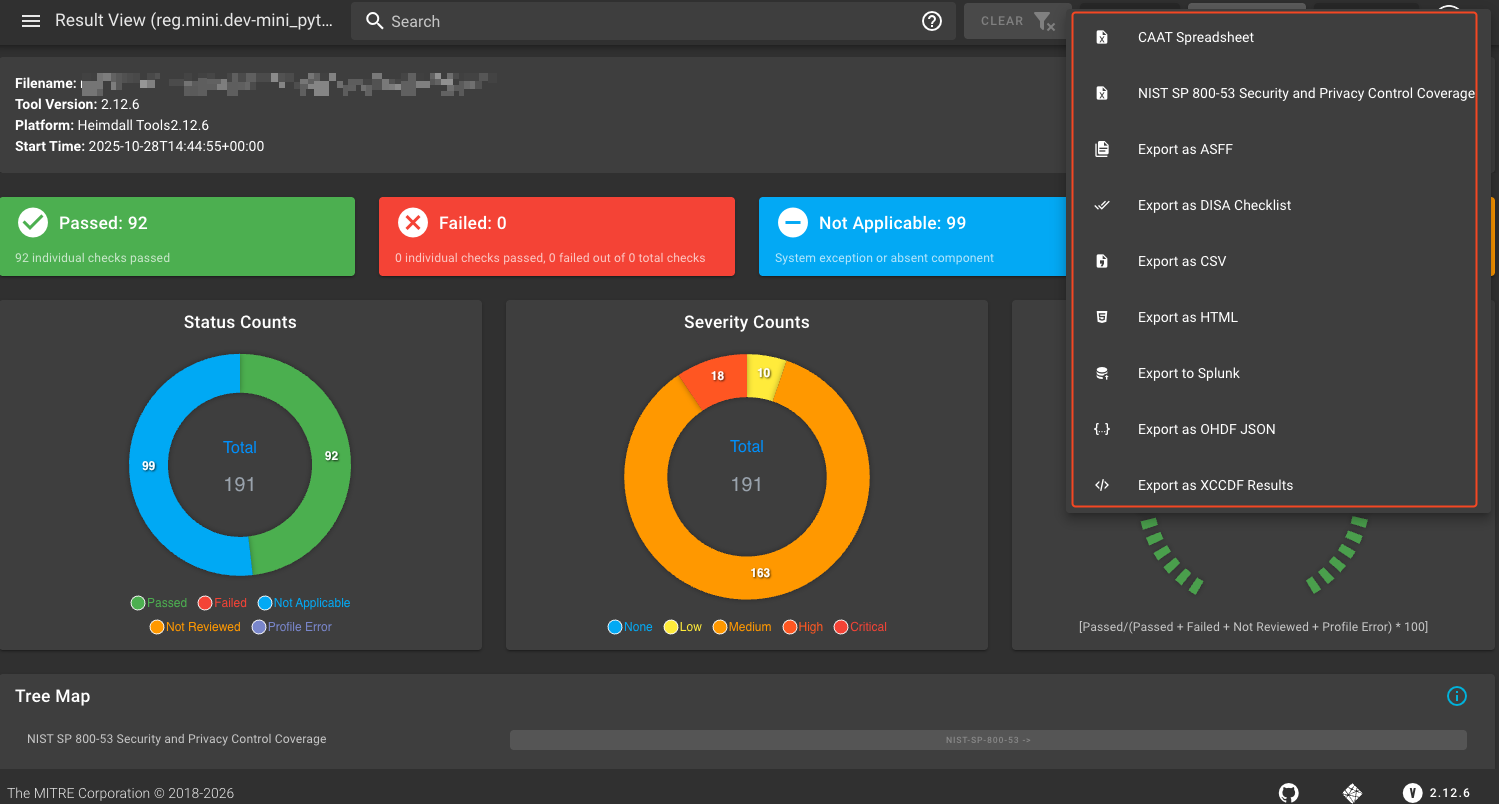
You can convert DISA STIG XML reports into other formats, as required, using a popular open-source tool from MITRE. This tutorial showcases examples using the heimdall-lite utility made available by the MITRE Security Automation Framework (SAF). This guide explains how to run the utility as a container in order to convert a DISA STIG XML report provided by Minimus into other common formats, including JSON, CSV, HTML, DISA Checklist, etc. MITRE Heimdall (https://github.com/mitre/heimdall2) is a suite of tools that provide a centralized visualization and reporting solution for automated security scan results.Pre-requisites
- Scan results obtained in XML format by running the Minimus OpenSCAP image. See the quick start guide
- Container runtime environment (such as Podman or Docker)
- Ability to pull in the heimdall-lite docker image to its execution location
- The heimdall-lite docker image currently ships for amd64 images only. If needed, you can use emulation as a workaround for other architectures such as macOS Darwin.
Run Heimdall Lite locally on macOS
Install Heimdall-Lite prerequisites
Since Heimdall Lite only ships in amd64 formats, the container image will either need to run on an x86 architecture or be passed through an emulator.This can be achieved on macOS Darwin by installing an emulator to pass through this image with an option such as
qemu. qemu may be installed locally with Homebrew:Pull the container image locally
Note - this pull will fail locally on Darwin if the platform flag is not included.
Connect to the running heimdall application
Open your local web browser to point at 
localhost:8080 (This example assumes you bound port 8080 but you should use the port you bound in the run command).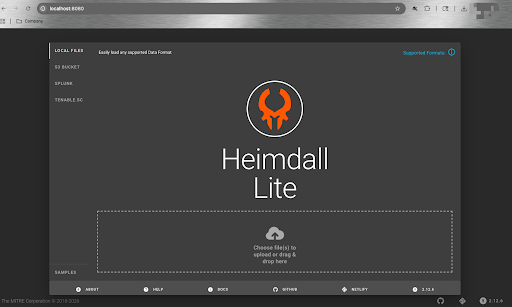
Upload XML file from OpenSCAP
Select Choose files to upload and select your XML file (that is the report generated using OpenSCAP).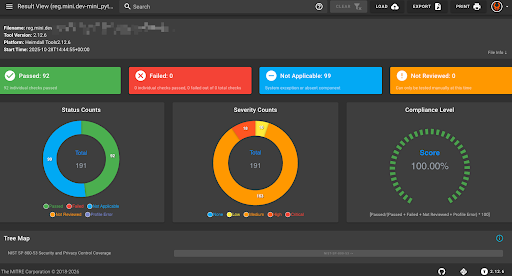
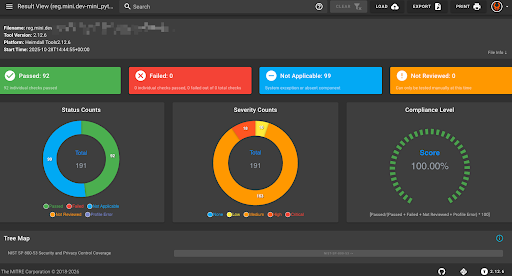
You will see the same matching checks previously noted from running OpenSCAP.
Run Heimdall Lite on a Cloud VM
This example showcases running Heimdall Lite on a GCP VM but the concept is the same for other cloud providers.Create a VM in your target cloud environment
Create a VM with Docker or Podman installed to execute the runtime of a container image that is x86-64 or amd64 based.
Create an SSH tunnel to the VM
To run the browser locally, you must now create an SSH tunnel to the instance and map it to the respective port the container is listening on. This can be done by using the Google Cloud CLI (
gcloud CLI) and then authenticating to your respective project where the VM is running.-
Authenticate to your GCP project via CLI:
-
Authenticate via web browser:
You may need to allow permissions from GCP. If successful, you will see the same success message in your local terminal:
Your browser has been opened to visit.
-
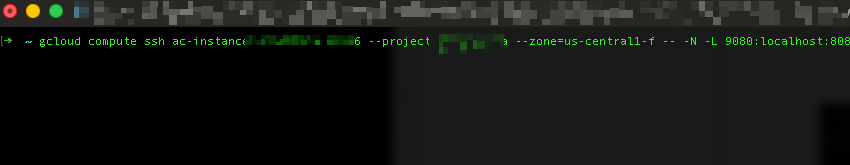
Create your SSH tunnel using gcloud:
You will need to update the command with the following:
- LOCAL_PORT - Use the port you enter in your local browser on your machine
- REMOTE_PORT - Use the port the Heimdall Lite container is bound to listen on in the cloud VM.
-
If run for the first time, you may be prompted to generate SSH keys locally. When successful, you will have an active process with this open tunnel and the cursor will be active.
Access the Heimdall Lite container from your local browser
Access the Heimdall Lite container from your local browser by typing in 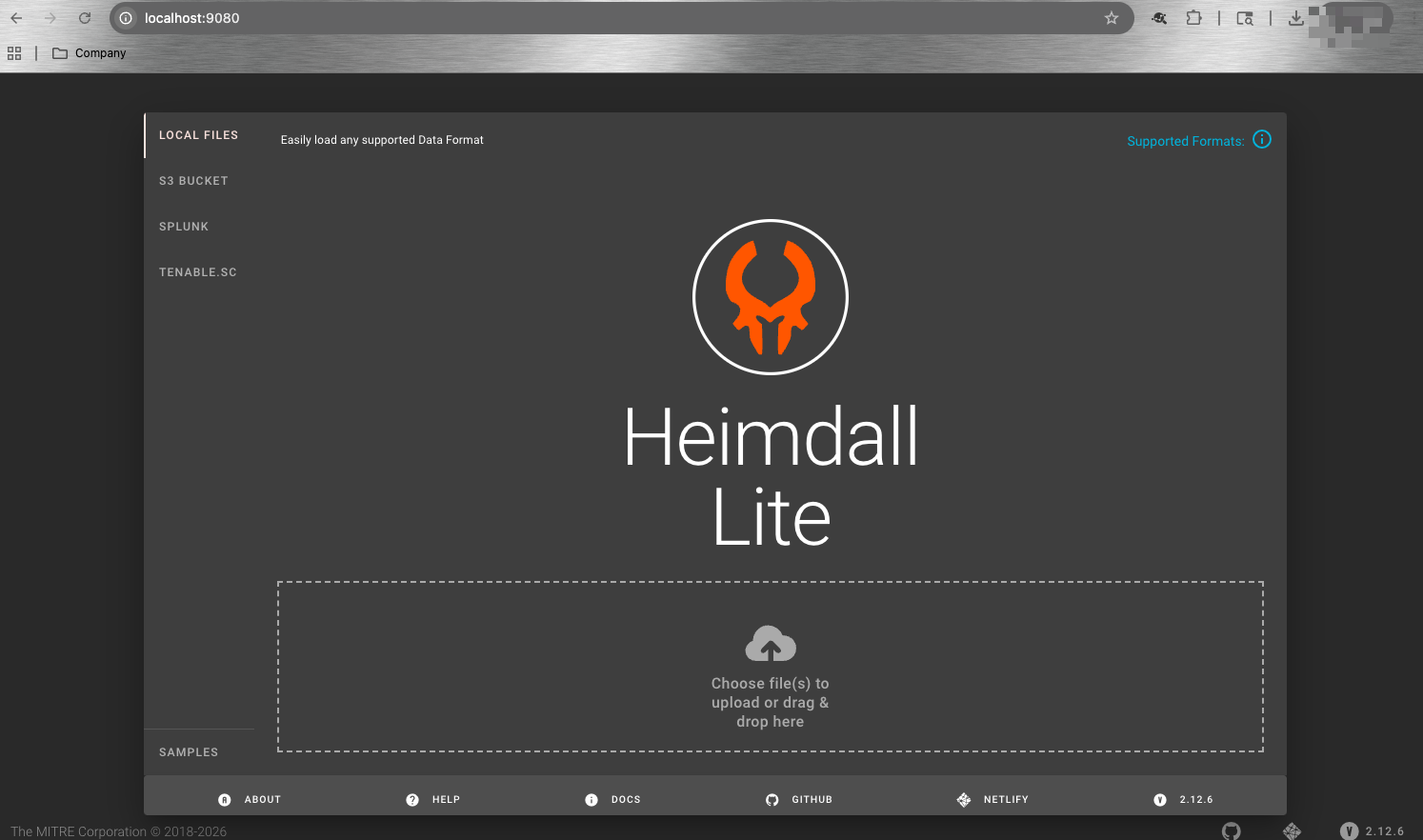
localhost:LOCAL_PORT, for example, localhost:9080.